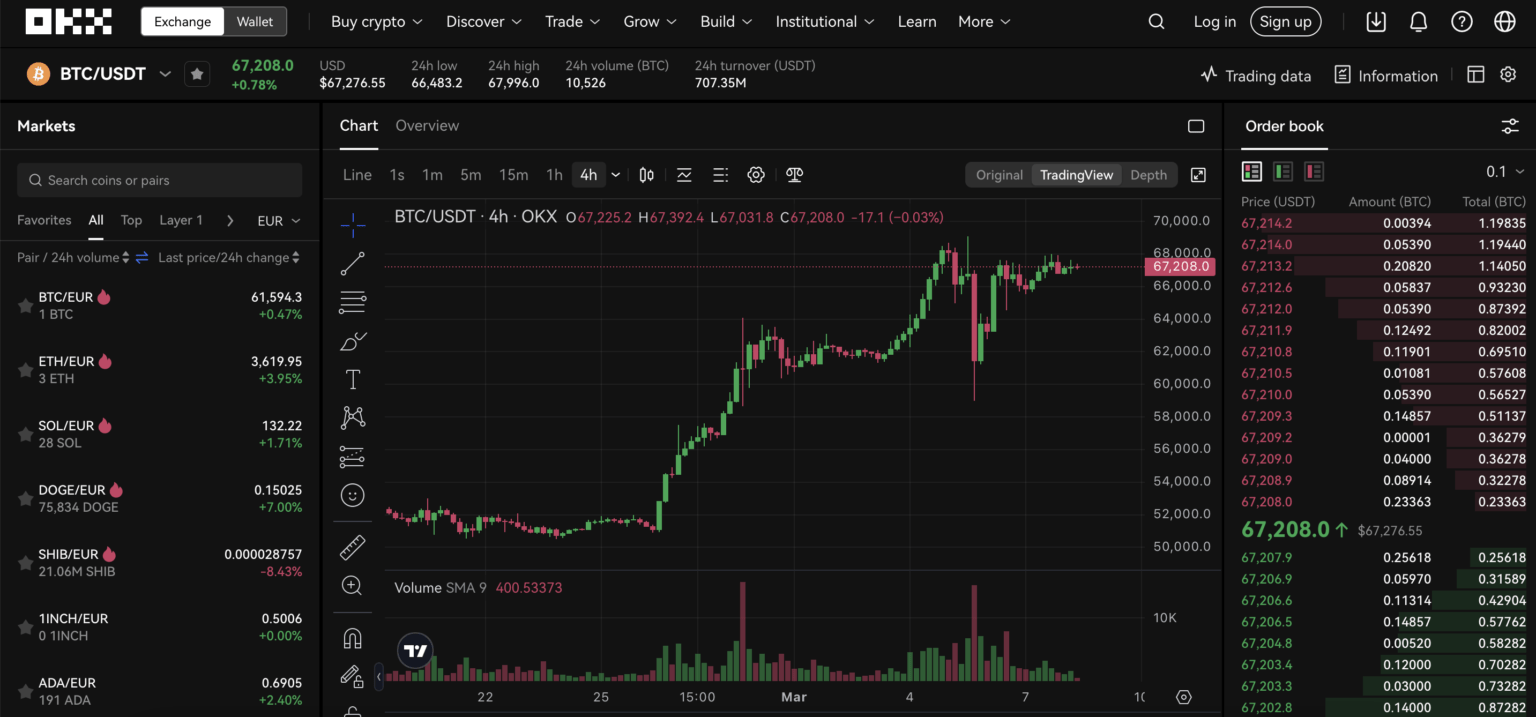
Many experienced traders treat login as a trivial step between intention and execution: type email, enter password, trade. That’s a misconception. On modern exchanges like OKX, the login is both an authentication protocol and a security control that gates access to custody, leveraged positions, staking, and cross-chain tooling. Treating it as a checkbox ignores layered risks—phishing, account takeovers, regulatory friction—and misses opportunities to design a safer, more flexible workflow.
This article explains how OKX’s sign-in mechanism works in practice for U.S.-based traders, why the combination of centralized and non-custodial features matters, where the system breaks, and practical heuristics you can use right now to reduce risk without losing agility.
Mechanics: what happens when you enter credentials
At the protocol level, OKX blends standard credential authentication with device and behavioral signals. You start with an identifier (email or phone) and a password. The server then evaluates additional factors: known device fingerprints, geolocation patterns, and AI-driven anomaly detection. If a session looks unusual, risk engines raise the authentication level and request mandatory Two-Factor Authentication (2FA) or a biometric prompt from the mobile app.
Two important technical mechanisms read through here. First, adaptive authentication: the system scales security friction based on detected risk rather than uniformly forcing high-friction steps on every login. Second, separation of custody: signing into the centralized exchange (CEX) and unlocking a non-custodial Web3 wallet are separate actions. That design lets you keep funds in the CEX while using a self-custodial wallet for on-chain interactions and DApps.
How OKX integrates custody, Web3 wallets, and login flows
OKX supports both a centralized account holding deposited assets and a self-custodial Web3 wallet where private keys live with the user. The Web3 wallet uses a seed phrase and supports hardware integrations (Ledger, Trezor). These two models coexist: signing into the exchange unlocks CEX features, while connecting the Web3 wallet to that account is an explicit, separate action—often performed via a browser extension or mobile deep link.
For US traders this split has practical consequences. Regulatory KYC (identity verification) is mandatory for exchange accounts: submitting a government ID and completing a facial liveness check are part of onboarding. That means some privacy-related use cases common in other jurisdictions—anonymous deposit/withdrawal—are constrained. Meanwhile, the non-custodial wallet preserves anonymity and user control, but it also places sole responsibility on the trader for seed management: lose the seed, lose access permanently.
Login protections and their limitations
OKX advertises military-grade encryption, AI-driven threat detection, and mandatory 2FA. Mechanistically, those are strong defenses: encrypted credentials at rest, behavioral AI to flag suspicious sessions, multi-factor prompts (SMS, Google Authenticator, biometrics) to prevent credential-only takeovers, and cold-storage for over 95% of on-exchange assets using multi-signature approvals for withdrawals.
Limitations matter: SMS 2FA, while convenient, is vulnerable to SIM swap attacks. Biometric login is strong on device but depends on device security; a compromised phone can still offer an attack vector. AI threat detection reduces false negatives but can produce false positives, temporarily blocking legitimate logins during travel or after rapid IP changes. Also, Proof of Reserves (PoR) increases transparency about solvency, but it does not prevent market losses or guarantee individual account recoverability in legal freezes or compliance actions.
Practical trade-offs for traders: convenience versus control
There are three realistic sign-in patterns traders choose between: convenience-first, security-first, and hybrid.
Convenience-first: low friction—email/password plus SMS 2FA and saving device sessions. Pros: fast order execution and mobile-first trading. Cons: higher exposure to social engineering and SIM-based theft.
Security-first: hardware 2FA (authenticator apps or U2F keys), no saved sessions, segregated accounts for staking vs trading, and keeping most funds in cold storage or the non-custodial wallet. Pros: reduced attack surface. Cons: slower reaction in fast markets and more cognitive overhead.
Hybrid: keep a small, hot trading balance on the CEX for active trades and move reserves to the cold store or the Web3 wallet (seed-protected + hardware). Use adaptive login: allow trusted devices but require re-authentication for key actions like withdrawals, margin changes, or high-leverage positions. For many US traders this hybrid balances compliance (KYCed accounts) with minimized custody risk.
Where the login process breaks and what to watch
Most failures fall into predictable categories: phishing and credential reuse; lost or compromised 2FA; travel-triggered lockouts; and interface confusion when linking CEX accounts with the non-custodial wallet. Phishing remains the most common root cause—attackers mimic login pages and intercept credentials. The defense is behavioral: never follow emailed login links; always navigate to the exchange directly or use a trusted bookmark. Set withdrawal whitelist addresses where available.
Account verification failures are another friction point for U.S. users. KYC systems can fail if documents are expired, photos are poor, or the liveness check fails. Plan ahead: verify identity well before you intend to move large sums or trade in regulated instruments. Finally, smart-contract interactions through the Web3 wallet carry different risk modes—approve-permission prompts must be read carefully because on-chain approvals can authorize token drains.
Decision-useful heuristics and a simple workflow
Here are four actionable heuristics you can adopt immediately:
1) Keep three buckets: hot (trading), warm (staking, short-term yield), and cold (long-term reserves). Limit the hot bucket to what you can tolerate losing overnight without liquidating positions.
2) Use an authenticator app or hardware key for 2FA. Reserve SMS only as a backup and monitor carrier security options (PINs, port freeze).
3) Treat the Web3 wallet seed like a will: offline, multiple copies, hardware-secured where possible. Use the non-custodial wallet when interacting with DApps and cross-chain swaps to avoid exposing exchange-held assets to smart contract risk.
4) When logging in from a new device, expect a friction window—plan trades accordingly. If you need instant execution while traveling, pre-authorize a trusted device and set session expiration to a sensible limit rather than indefinite.
For step-by-step guidance to the OKX web login and specific UI prompts, see this walkthrough: okx login.
Short what-to-watch list (near-term signals)
1) Delisting campaigns: exchanges periodically remove low-liquidity pairs. Recent delistings (this week) signal ongoing marketplace hygiene—check announcements before building large exposures in thin assets.
2) Regulatory changes in the U.S.: evolving AML or crypto custody rules can alter KYC depth and withdrawal policies. Monitor official OKX notices and adjust onboarding timing for large transfers.
3) Cross-chain and DEX aggregator risk: as OKX routes liquidity across many chains and DEXs, watch for smart contract audits and bridge security updates. Increased aggregator usage improves pricing but concentrates dependency on fewer bridging protocols.
FAQ
Q: If I lose access to my OKX account, what recovery options exist?
A: Recovery typically relies on account-level recovery flows tied to your KYC identity: email verification, ID checks, and possibly live support. For non-custodial wallets, recovery depends solely on your seed phrase—if it’s lost there is no platform recovery. This is a crucial boundary: exchange accounts can be reinstated with institutional processes; self-custodial wallets cannot.
Q: Is biometric login safe enough for high-frequency trading?
A: Biometric login (on-device) is convenient and strong against remote attacks, but it depends on device hardware security. For high-frequency, high-stakes trading, pair biometrics with hardware 2FA or U2F keys and keep a separate hot wallet with only necessary capital for execution speed.
Q: Should I connect my OKX Web3 wallet to every DApp I use?
A: No. Connect selectively and use per-DApp accounts when possible. Approve minimal token allowances and revoke approvals after use. Remember that on-chain approvals can be permanent until explicitly revoked and can lead to token drains if you grant excessive permissions.
Login is not a single button press; it’s a control plane that shapes custody, compliance, and trading agility. For U.S. traders the right balance is rarely the extremes: guard your seed, prefer hardware-based 2FA, use adaptive sessions for trusted devices, and keep a clear plan for hot versus cold capital. That combination preserves execution speed while containing the most common operational and security risks.